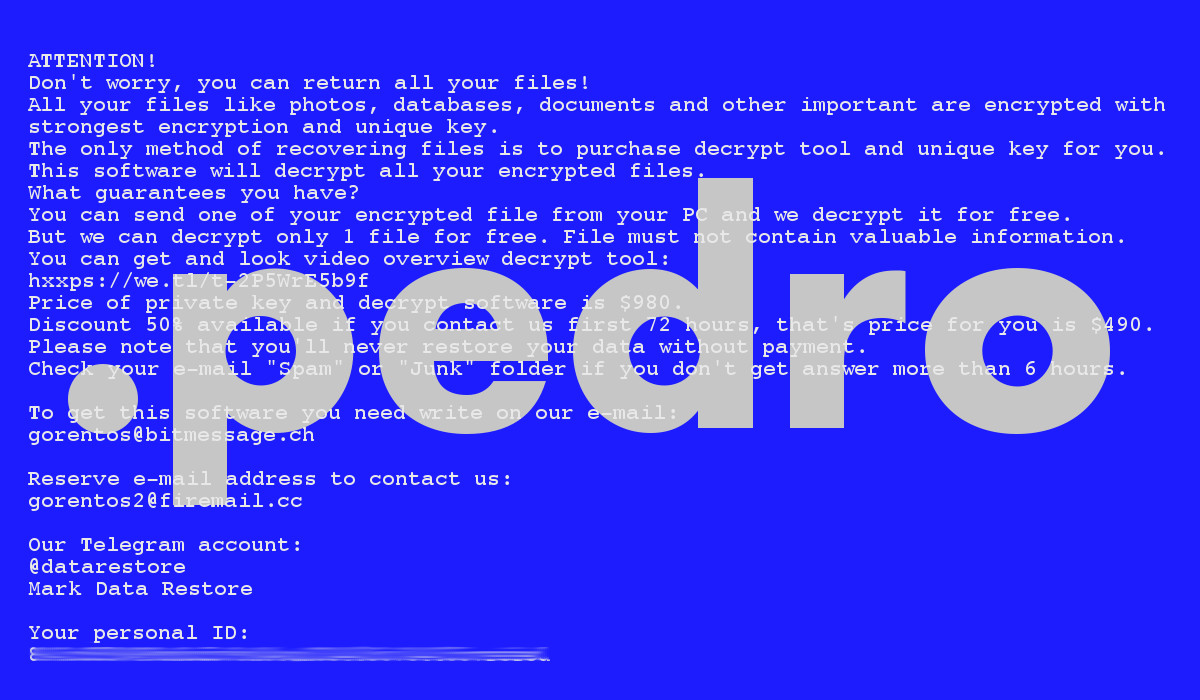
Pedro is designed to lock away your files before demanding you to pay a ransom of $980 to get them back. Pedro being the name of this virus, after the bit that is attached to the names of your locked files — “.pedro”. This is a new version of a familiar malware strain, STOP/Djvu. It’s known for being actually harmful and the victims who don’t have backups of their data risk actually losing their data permanently.
Pedro Ransomware quicklinks
- What is Pedro ransomware
- Pedro infection symptoms
- Pedro spreading methods
- How to deal with Pedro
- How to remove Pedro
- Automatic Malware removal tools
- How to restore the files
- How to recover Pedro Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Pedro Ransomware encrypted files
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
So, what are your options? Well, first it’s important to make the malware go away, for example, using antivirus. Pedro probably brought a password-stealer along, so don’t use your infected computer to access any important accounts online. Then, you can think about restoring your files, which is not 100% possible, but a few options do exist, such as backups, data recovery, and STOPDecrypter. Finally, you need to fix the damage that Pedro has done to your settings, such as fixing your antivirus program after the ransomware broke it.
What is Pedro ransomware
Pedro infection symptoms
Ransomware comes in various flavors, like TotalWipeOut (which must have been a work in progress), JeepersCrypt (which was swiftly solved and decrypted), and Sodinokibi (which exploited a recently-discovered security flaw to infect certain servers).
Pedro ransomware is a virus that tries to convince the owners of the infected computer to pay a few hundred dollars by cryptographically locking the files on that computer and then threatening to never give the key to unlock the files unless paid. The reason why the infected computer is even functional after a Pedro infection is that the files needed by the Operating System are left untouched.
If you noticed your files being renamed from something like “picture.jpg” to “picture.jpg.pedro”, if you found the “_readme.txt” note left in one of your folders, then the Pedro ransomware has, unfortunately, infected your device.
By the way, if you don’t see file extensions, just change the settings: Windows 10 — by selecting “View” in the menu in File Explorer and check “File name extensions”, Windows 7 — expand “Organize”, click on “Folder and search options”, select “View”, then uncheck “Hide extensions…”.
Pedro spreading methods
One way that Pedro is spread is using pirated files. Activators, cracked programs like Windows activators downloaded through shady links and guides shared on social media and forums, or keygens and unlocked expensive commercial programs downloaded from the wrong website can easily be infected with Pedro or other malware. It’s not a myth that nongenuine software has a high chance to be infected with malware, people have looked into it.
Malicious spam is also used to spread Pedro. Phishing emails that are made to look like a message from a co-worker, an update on a missed parcel, an urgent invoice — these are sent out to thousands of recipients, with the virus attached. Only the minority of the recipients will fall for these deceptive emails, but that’s enough for Pedro.
Pedro likely brings along a trojan and credential stealer called AZORult, which is dangerous for how it could give some criminals a chance to hack your online accounts.
How to deal with Pedro
How to remove Pedro
Even though some people choose to wipe their infected disk to get rid of all malware, that shouldn’t be necessary. Manual or automatic removal of Pedro can work, though the manual way can be complicated and different in each case. But an anti-malware tool like Spyhunter would be able to find the malware for you.
That’s really not all, though. Pedro must have messed with your normal antivirus protection, you should repair the installation and/or update it. Additionally, check your hosts file because Pedro might have made some unwanted entries there. And don’t forget to make sure that 2-factor verification is working everywhere important, or even change your passwords.
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to restore the files
Since the best defense against ransomware is having file backups, restoring the encrypted data from backups would be ideal (though only after you have removed the virus).
The data restoring options described below are not guaranteed to work because they depend on your individual circumstances. They’re worth trying out if you have the time, but it might be work to make backup copies of the locked files before.
Lastly, a cybersecurity volunteer researcher Demonslay335 has developed a tool that, in certain circumstances (in the minority of cases), can completely reverse the encryption. If it doesn’t work for a supported STOP/Djvu version, then it doesn’t work. If Pedro is ever supported by the program, you should try running STOPDecrypter on the locked files.
How to recover Pedro Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Pedro Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Pedro Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Pedro Ransomware. You can check other tools here.Step 3. Restore Pedro Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Pedro Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Pedro Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








