Reqg is a file-locking virus. Once it’s on a computer, it encrypts various files (pictures, music, documents) so that they can no longer be opened. Reqg then asks for hundreds of dollars to fix these files.
Reqg can be deleted with antivirus programs, but this doesn’t decrypt (fix) the files that were broken. To do that, other solutions are needed.
Reqg File Locker quicklinks
- The symptoms of infection by Reqg
- How does Reqg infect computers?
- What about your files?
- How to delete Reqge
- Important -- edit the hosts file to unblock security websites
- Find and edit the hosts file
- Download and run the antivirus program
- Automatic Malware removal tools
- How to recover Reqg File Locker encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Reqg File Locker encrypted files
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
About Reqg ransomware:
| Threat type | File encrypting ransomware,
trojan. |
|---|---|
| How Reqg infects computers | It spreads on piracy sites,
it encrypts files and changes their names, it deletes backups and blocks cybersecurity sites. |
| Can you get your data back? | Restore your files from backups,
or use the free decryption tool to check whether free decryption is possible, consider other options. |
| How to delete Reqg | Find and delete malicious programs and files with antivirus scanners (Spyhunter others). |
The symptoms of infection by Reqg
When Reqg attacks a computer, it changes file names by appending “.reqg” – file names have double extensions. This causes Windows to show these files’ icons as blank pages.
Here are some other things that the Reqg virus does:
- Before changing file names, Reqg ransomware encrypts those files. This basically scrambles file contents. It happens very quickly, so by the time you notice it, it’s already too late.
- It deletes backups to stop victims from recovering their data.
- It blocks some websites, especially sites that are related to cybersecurity (including ours).
- Reqg deletes some antivirus data. Depending on which security program you have, this could break your antivirus (at least until you reinstall it).
- Other viruses could be installed together with Reqg.
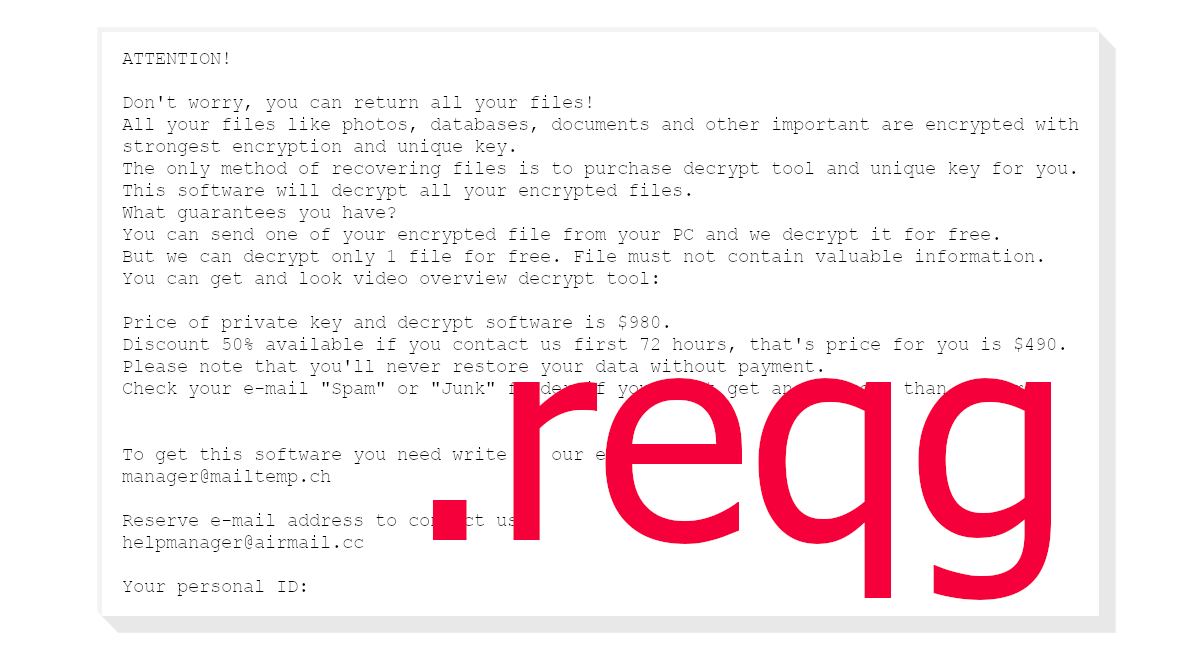
The virus also creates notes called “_readme” like pictured below. These notes give the email addresses (manager@mailtemp.ch and managerhelper@airmail.cc) of the criminals who are behind the Reqg virus.
How does Reqg infect computers?
The note is written in an ambiguous way, as though your files just happened to get encrypted. However, the same people who created the ransom note are also responsible for the Reqg infection.
Reqg is a variant of Djvu ransomware, similar to Nooa, Moqs, and hundreds of others. This extortion scheme has been going on for years. The criminals responsible for it must be making a lot of money for them to keep at it.
The Reqg virus gets uploaded on shady pirating sites and file sharing sites. Individual PC users and small businesses get infected when they try to install free (cracked) software.
Antivirus programs can help – they detect Reqg ransomware as Trojan, Malicious, Ransom, and other names (Virustotal.com). But when people pirate, they often disable their antivirus programs to stop them from interfering with cracking tools. This allows viruses to infect PCs unopposed.
What about your files?
Reqg encrypts user files. You can open an encrypted text file in Notepad and see what it looks like. Encrypted by Reqg, what used to be normal text would look like a soup of random symbols. Only some files (some archives, audio files, and others) can still be opened, but even they are partially corrupted.
The ransomware asks for up to $980. Unfortunately, there’s no easy way to fix the files without paying the ransom.
One possible solution can be found on Emsisoft.com. Scan your Reqg-locked files with this tool and it should tell you whether free decryption is possible.
Here’s the thing: there’s a small chance that Reqg failed to get a unique encryption key to lock your files and defaulted to a non-unique, so-called “offline” key. If that is true for you, if someone else who is in the same situation pays the ransom and gets the decryption key, and if they upload this key, then you could use it to unlock your files. Again, there’s a small chance of this happening, but it’s something.
There are a few other options that are worth looking into. But data backups are the best way to protect yourself from the Reqg virus and similar infections.
How to delete Reqge
Before you can use your computer normally again, you need to delete Reqg ransomware and other malware. You can scan your PC with an antivirus scanner, such as Spyhunter, and have it do the job. You can reset Windows and reformat your C drive. Even then, it’s still important to scan your PC and delete malicious files.
Normally, Reqg ransomware spreads on pirating sites. If you have an idea of where you got this malware, be careful of the place and don’t download suspicious files from there again.
At least not until you prepare for ransomware infections by making backups of your important data. That way, if ransomware infects your PC, you’ll be able to recover your files.
Important -- edit the hosts file to unblock security websites
TL DR : The hosts file is edited to block security sites Before the virus can be removed, it's necessary to fix the hosts file (the file which controls which addresses connect to which IPs). That is the reason the majority of security websites is inaccessible when infected with this particular parasite. This infection edits this file to stop certain websites, including anti-malware download sites, from being accessed from the infected computer, making browsers return the "This site can't be reached" error. Luckily, it's trivial to fix the file and remove the edits that were made to it.Find and edit the hosts file
The hosts file can be found on C:/Windows/System32/Drivers/etc/hosts. If you don't see it, change the settings to see hidden files.- In the Start Menu, search for Control Panel.
- In the Control Panel, find Appearance and Personalization.
- Select Folder Options.
- Open the View tab.
- Open Advanced settings.
- Select "Show hidden files...".
- Select OK.
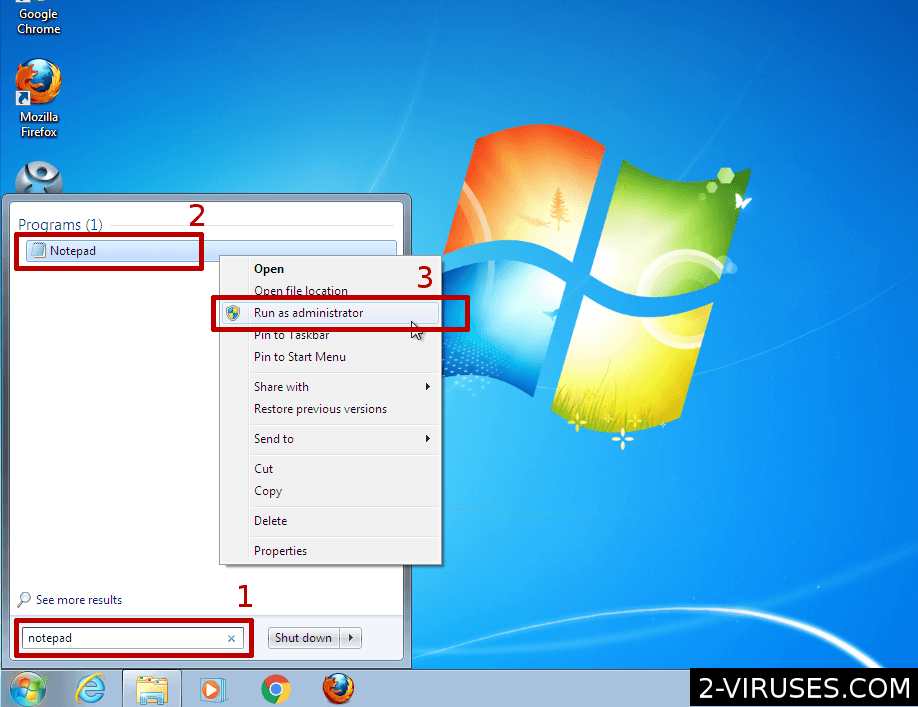
- Open the Start Menu and enter "notepad".
- When Notepad shows up in the result, right-click on it.
- In the menu, choose "Run as administrator"
- File->Open and browse for the hosts file.
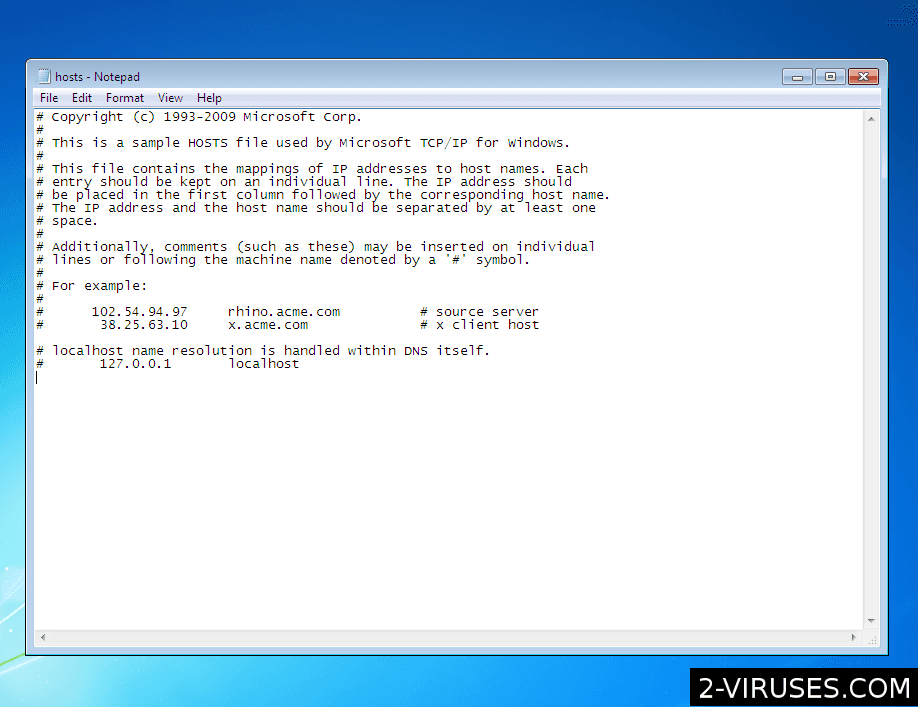 Delete additional lines that they connect various domain names to the wrong IP address. Save the file.
Delete additional lines that they connect various domain names to the wrong IP address. Save the file.
Download and run the antivirus program
After that, download antivirus programs and use them to remove the ransomware, the trojan, and other malware. Spyhunter (https://www.2-viruses.com/reviews/spyhunter/dwnld/).Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Reqg File Locker encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Reqg has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Reqg File Locker
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Reqg. You can check other tools here.Step 3. Restore Reqg File Locker affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Reqg tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Reqg File Locker encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








